Step 4 - Enable your AKS cluster to access Key Vault
There are two methods for authentication; select the one which applies to you:
- 4A - Managed identity (recommended)
- 4B - Service principal
- Use this method only if managed identities are not available or not desired in your cluster.
4A - Managed identity
If your AKS cluster was not created with managed identities, this can be added via:
az aks update -g "${rgp}" -n "${aksname}" --enable-managed-identity
To sync Key Vault secrets to Kubernetes secrets, the AKS kubelet identity needs get and list access to Key Vault.
- First, retrieve the object ID of the kubelet identity:
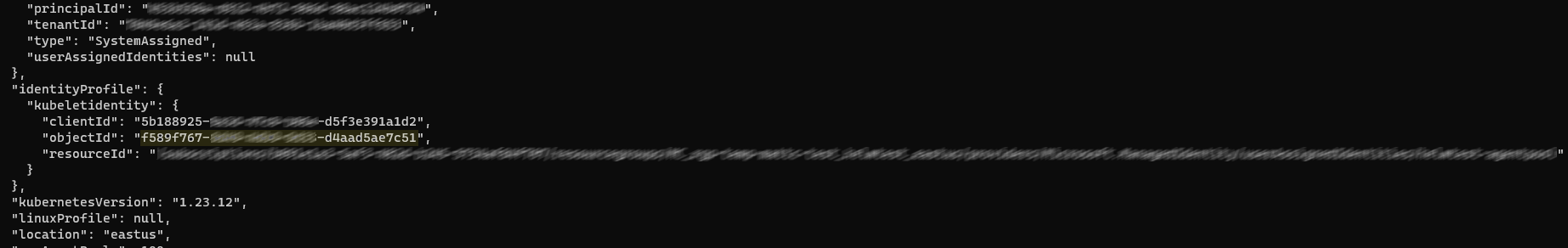
az aks show -g "${rgp}" -n "${aksname}"
This will return a large JSON response. Scroll until you find:
identityProfile → kubeletidentity → objectId
- Now set access permissions on the Key Vault:
az keyvault set-policy --name "${kvname}" --object-id "${objectid}" --secret-permissions get list
4B - Service principal
If you are using a service principal, you will need:
objectIdappIdtenantIdclientSecret
These can all be found in Azure Active Directory.
az keyvault set-policy --name "${kvname}" --object-id "${objectid}" --secret-permissions get list
- Create the Kubernetes secret:
kubectl create secret generic keyvault-service-principal \
--from-literal=ClientID="${appid}" \
--from-literal=ClientSecret="${clientsecret}"