Overview
As an alternative to cloud managed Kubernetes deployments, Glasswall Halo can be deployed in a single node configuration on traditional virtual machine infrastructure. This option is intended for on premises environments where cloud based infrastructure is not available or permitted.
Single node deployments consist of the following core components. For version details, refer to the Release Notes.
- Red Hat Enterprise Linux base operating system
- Rancher Kubernetes Engine Government (RKE2), a Cloud Native Computing Foundation certified Kubernetes distribution
- Glasswall Halo Helm charts and container images
To simplify deployment, preconfigured virtual machine images are available in OVA and VHD formats.
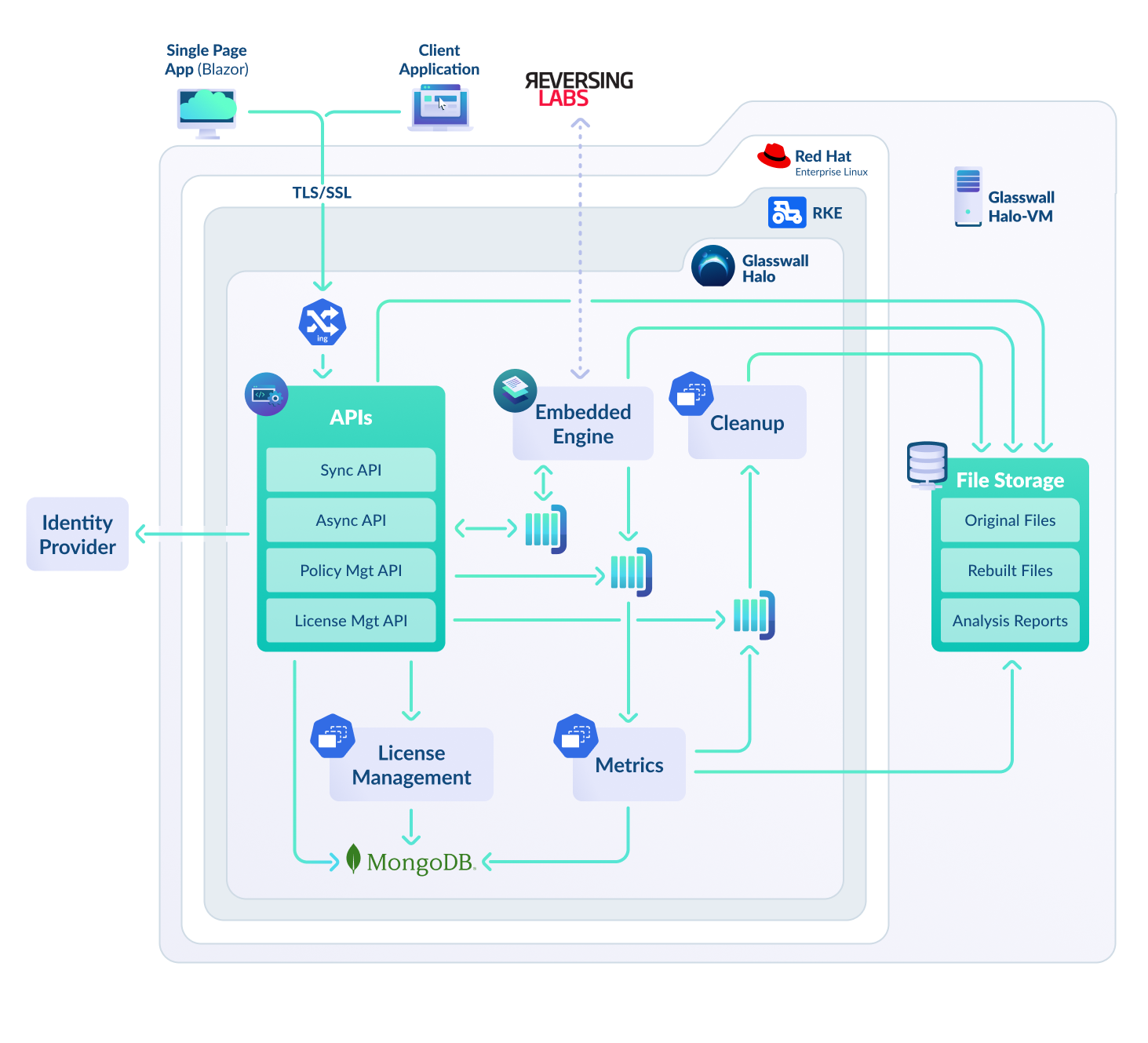
Architecture
Security posture
The following security hardening procedures have been applied to each of the core components of the virtual machine deployments.
-
Red Hat Enterprise Linux base operating system
- Hardened using the DoD Security Technical Implementation Guides (STIGs) for Red Hat Enterprise Linux
-
Rancher Kubernetes Engine Government (RKE2)
-
Glasswall Halo Helm charts and container images
- In line with standard Glasswall Halo deployments, all Helm charts and container images undergo continuous SCA, SAST, DAST, IaC, and container security scanning, along with associated patching
Security reports generated from these hardening procedures are available on request.
Current limitations of single node VM deployments
In a single node deployment, scalability is limited by the capacity of the target virtual machine. The deployment dynamically allocates the appropriate number of engines based on the available resources of the underlying VM.